Jewel Co is setting up an online business importing and selling jewellery headphones. The cost of each set of headphones varies depending on the number purchased, although they can only be purchased in batches of 1,000 units. It also has to pay import tax
题目
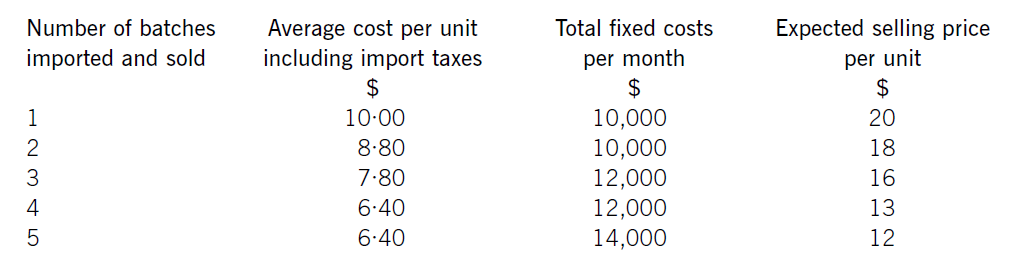
Jewel Co is setting up an online business importing and selling jewellery headphones. The cost of each set of headphones varies depending on the number purchased, although they can only be purchased in batches of 1,000 units. It also has to pay import taxes which vary according to the quantity purchased.
Jewel Co has already carried out some market research and identified that sales quantities are expected to vary depending on the price charged. Consequently, the following data has been established for the first month:
Required:
(a) Calculate how many batches Jewel Co should import and sell. (6 marks)
(b) Explain why Jewel Co could not use the algebraic method to establish the optimum price for its product.
(4 marks)
相似考题
更多“Jewel Co is setting up an online business importing and selling jewellery headphones. The cost of each set of headphones varies depending on the number purchased, although they can only be purchased in batches of 1,000 units. It also has to pay import tax”相关问题
-
第1题:
(b) Write a letter to Joanne setting out the value added tax (VAT) registration requirements and advising on
whether or not she should or could register for VAT and if registered if she could recover the VAT suffered on
the consultancy fees and computer purchased in October 2005. (7 marks)
正确答案:
(b) [Joanne’s address] [Firm’s address]
Dear Joanne 5 February 2006
I am writing to you in order to set out the value added tax (VAT) issues you face on registering your trade, together with some
other aspects of VAT that are relevant to you.
Registration
VAT registration is compulsory once taxable supplies exceed £58,000. This turnover figure is based on the value of your
cumulative taxable supplies in the previous 12 months. You have an obligation to inform. Customs within 30 days of the end
of the month in which the annual limit is exceeded. Registration will become effective on the first day of the following month.
VAT registration is also required if there are reasonable grounds for believing that the taxable supplies in the following 30 days
will exceed £58,000. In such cases, notification is required by the end of that 30 day period with registration being effective
from the start of that period.
Based on your estimates of taxable supplies, you will exceed the annual limit in October 2006 when your cumulative turnover
will be £62,000. You will therefore have to inform. Customs by the end of November. Your registration will be effective as of
1 December 2006.
You also have the option of voluntarily registering prior to then in which case you will normally become registered from the
date you applied. This is useful where your sales are to VAT registered customers for whom the extra VAT would not be a cost.
You would then be able to recover VAT on your attributable costs. However, you will have to comply with the VAT
administrative requirements.
Recovery of pre-registration VAT
It is possible to claim the recovery of VAT incurred prior to registering for VAT. There are some conditions, however. The costs
of the goods or services must have been incurred for the purpose of the business and there are time limits. You have three
years from the effective date of registration to recover the VAT on fixed assets (such as your computer) but only six months in
the case of purchased services (such as the consultancy fees).
As a result, I would recommend that you apply for voluntary registration as soon as possible, as registering after 1 April 2006
will mean that you will be unable to reclaim the VAT on your consultancy fees.
I hope the above information is useful to you.
Yours sincerely,
A. Consultant. -
第2题:
Which statements are true regarding ISDN channels?()A. Each B channel can transmit up to 64 kbps
B. The ISDN B channel carries voice or data
C. The ISDN D channel transmits control information.
D. The D channel transmission rate varies depending on the service used.
E. HDLC or PPP can be used to encapsulate D channel information.
参考答案:A, B, C
-
第3题:
Which are three advantages of PPPoA implementation? ()
- A、NAP and NSP provide secure access to corporate gateways without managing end-to-end PVCs.NAP and NSP use Layer 3 routing,Layer 2 Forwarding,or Layer 2 Tunneling Protocol tunnels.Hence,they can scale their business models for selling wholesale service
- B、The NSP can oversubscribe by deploying idle and session timeouts using an industry standard RADIUS server for each subscriber
- C、Only a single session per CPE on one virtual channel (VC).The username and password are configured on the CPE, so all users behind the CPE for that particular VC can access only one set ofservices. Users cannot select different sets of services, although using multiple VCs and establishing different PPP session on different VCs is possible
- D、If a single IP address is provided to the CPE, and NAT or PAT is implemented,certain applications such as IPTV,which embed IP information in the payload, well not work. Additionally,if an IP subnet feature is used,an IP address also has to be reserved for the CPE
- E、PPPoA can use the features on the Cisco Service Selection Gateway (SSG)
正确答案:A,B,E -
第4题:
The number of Congressmen from each state varies depending on ()
- A、the size of the area
- B、the size of the population
- C、the tradition
- D、the wealth
正确答案:B -
第5题:
An administrator has purchased monitoring software that can be configured to alert administrators when hardware and applications are having issues. All devices are configured with SNMP, but the administrator wants to further secure the SNMP traffic. Which of the following settings would BEST provide additional monitoring security?()
- A、Setting up a custom community name
- B、Configuring the network to block traffic on port 161
- C、Configuring the Windows Firewall to block port 161
- D、Setting SNMP to read only on the devices
- E、Installing new MIBs
正确答案:D,E -
第6题:
A customer is installing a new x3850 X5 server and has purchased a warranty upgrade on the server to 24 x 7 four hour response. The customer requested IBM help with setting up the RAID adapter. The customer was told IBM would not help them. Which of the following should be verified first?()
- A、The customer used their IBM Customer Number
- B、The customer has activated their base warranty
- C、The customer purchased Remote Technical Support Servicepac
- D、The customer escalated the issue to the Duty Manager
正确答案:C -
第7题:
A company has a business application that provides its users with many different reports: receivables reports, payables reports, revenue projects, and so on.The company has just purchased some new, state-of-the-art,wireless printers, and a programmer has been assigned the task of enhancing all of the reports to use not only the company’s old printers, but the new wireless printers as well.When the programmer starts looking into the application, the programmer discovers that because of the design of the application, it is necessary to make changes to each report to support the new printers. Which two design concepts most likely explain the situation?()
- A、Inheritance
- B、Low cohesion
- C、Tight coupling
- D、High cohesion
- E、Loose coupling
- F、Object immutablility
正确答案:B,C -
第8题:
ABC Corp. has set up the Asset Category key flexfield. It has also set up a descriptive flexfield tostore vehicle information associated with the asset category "Vehicle." Identify two correctstatements.() (Choose two.)
- A、The setting up of the descriptive flexfield is mandatory.
- B、The Asset Category flexfield is owned by the Oracle Assets module.
- C、The descriptive flexfield is associated with tables in the Oracle Assets module.
- D、Only the Asset Category flexfield is associated with tables in the Oracle Assets module.
正确答案:B,C -
第9题:
单选题The number of Congressmen from each state varies depending on ()Athe size of the area
Bthe size of the population
Cthe tradition
Dthe wealth
正确答案: C解析: 暂无解析 -
第10题:
多选题A company has a business application that provides its users with many different reports: receivables reports, payables reports, revenue projects, and so on. The company has just purchased somenew, state-of-the-art, wireless printers, and a programmer has been assigned the task of enhancing all ofthe reports to use not only the company’s old printers, but the new wireless printers as well. When the programmer starts looking into the application, the programmer discovers that because of the design of theapplication, it is necessary to make changes to each report to support the new printers. Which two designconcepts most likely explain this situation? ()AInheritance
BLow cohesion
CTight coupling
DHigh cohesion
ELoose coupling
FObject immutability
正确答案: A,F解析: 暂无解析 -
第11题:
单选题A customer is installing a new x3850 X5 server and has purchased a warranty upgrade on the server to 24 x 7 four hour response. The customer requested IBM help with setting up the RAID adapter. The customer was told IBM would not help them. Which of the following should be verified first?()AThe customer used their IBM Customer Number
BThe customer has activated their base warranty
CThe customer purchased Remote Technical Support Servicepac
DThe customer escalated the issue to the Duty Manager
正确答案: A解析: 暂无解析 -
第12题:
单选题Squeaky Beans Inc. hired an outside consultant to develop their web application. To finish the job quickly,the consultant created several dozen JSP pages that directly communicate with the database. The Squeakybusiness team has since purchased a set of business objects to model their system, and the Squeaky developer charged with maintaining the web application must now refactor all the JSPs to work with the newsystem. Which pattern can the developer use to solve this problem?()ATransfer Object
BService Locator
CIntercepting Filter
DBusiness Delegate
正确答案: C解析: 暂无解析 -
第13题:
ABC Corp. has set up the Asset Category key flexfield. It has also set up a descriptive flexfield tostore vehicle information associated with the asset category "Vehicle." Identify two correctstatements.() (Choose two.)
A.The setting up of the descriptive flexfield is mandatory.
B.The Asset Category flexfield is owned by the Oracle Assets module.
C.The descriptive flexfield is associated with tables in the Oracle Assets module.
D.Only the Asset Category flexfield is associated with tables in the Oracle Assets module.
参考答案:B, C
-
第14题:
Which of the following statements regarding ISDN are correct?()A. Each ISDN B channel has transmission speeds of up to 64 kbps.
B. The ISDN B channel can carry video, voice or data.
C. The ISDN B channel transmission rate varies depending on the service used.
D. The ISDN D channel transmits control information.
E. The ISDN B channels can be configured with different subnets and encapsulation types when dialer profiles are configured.
参考答案:A, B, D
-
第15题:
Squeaky Beans Inc. hired an outside consultant to develop their web application. To finish the job quickly, the consultant created several dozen JSP pages that directly communicate with the database. The Squeaky business team has since purchased a set of business objects to model their system, and the Squeaky developer charged with maintaining the web application must now refactor all the JSPs to work with the new system. Which pattern can the developer use to solve this problem?()
- A、 Transfer Object
- B、 Service Locator
- C、 Intercepting Filter
- D、 Business Delegate
正确答案:D -
第16题:
Which statements are true regarding ISDN channels?()
- A、Each B channel can transmit up to 64 kbps
- B、The ISDN B channel carries voice or data
- C、The ISDN D channel transmits control information.
- D、The D channel transmission rate varies depending on the service used.
- E、HDLC or PPP can be used to encapsulate D channel information.
正确答案:A,B,C -
第17题:
A customer wants to run DB2 on a Power 780 with uncapped partitions. They have licensed DB2 for 32 of the 64 active cores, and will use it in multiple partitions. How can the customer ensure that the number of licenses purchased for DB2 is not exceeded?()
- A、Create a 32-core shared processor pool for the DB2 partitions.
- B、Limit the number of virtual processors on each DB2 partition to 32.
- C、Use the IBM License Metric Tool to dynamically manage DB2 usage in the partitions.
- D、Set the ‘Desired Processing Units’ in each DB2 partition profile so that the sum of all partitions equals 32.
正确答案:A -
第18题:
The System Administrator has set up shared processors on three partitions in the p5 590 system. The shared processors have been set to uncapped. The system administrator notices that the logical partition is acting like it is capped. What is the most probable cause?()
- A、The uncapped weight has been set to 0.
- B、The uncapped weight has been set to 128.
- C、The processing unit for that partition was set to .1 processing units. A full processor was assigned.
- D、The processing unit for that partition was set to 0.50 processing units. A full processor was assigned.
正确答案:A -
第19题:
Squeaky Beans Inc. hired an outside consultant to develop their web application. To finish the job quickly,the consultant created several dozen JSP pages that directly communicate with the database. The Squeakybusiness team has since purchased a set of business objects to model their system, and the Squeaky developer charged with maintaining the web application must now refactor all the JSPs to work with the newsystem. Which pattern can the developer use to solve this problem?()
- A、Transfer Object
- B、Service Locator
- C、Intercepting Filter
- D、Business Delegate
正确答案:D -
第20题:
问答题Judy plans to visit the National Gallery once each month in 2012 except in July and August when she plans to go three times each. A single admission costs $3.50, a pass valid for unlimited visits in any 3-month period can be purchased for $18, and an annual pass costs $60.00. What is the least amount, in dollars, that Judy can spend for her intended number of visits? dollars正确答案: 49.50解析:
根据题干可知,2012年,Judy共打算参观国家美术馆 16 次,那么根据题意,每次都购买入馆费的话需要花费16×$3.50=$56,这显然比办理年卡($60.00)花费少;假如Judy在6-8月期间办理月卡,其余月份每次支付入馆费,那么她的总花费为$18+(9×$3.50)=$49.50;由此可见,最少的花费为$49.50。 -
第21题:
多选题An administrator has purchased monitoring software that can be configured to alert administrators when hardware and applications are having issues. All devices are configured with SNMP, but the administrator wants to further secure the SNMP traffic. Which of the following settings would BEST provide additional monitoring security?()ASetting up a custom community name
BConfiguring the network to block traffic on port 161
CConfiguring the Windows Firewall to block port 161
DSetting SNMP to read only on the devices
EInstalling new MIBs
正确答案: D,E解析: 暂无解析 -
第22题:
多选题Which are three advantages of PPPoA implementation? ()ANAP and NSP provide secure access to corporate gateways without managing end-to-end PVCs.NAP and NSP use Layer 3 routing,Layer 2 Forwarding,or Layer 2 Tunneling Protocol tunnels.Hence,they can scale their business models for selling wholesale service
BThe NSP can oversubscribe by deploying idle and session timeouts using an industry standard RADIUS server for each subscriber
COnly a single session per CPE on one virtual channel (VC).The username and password are configured on the CPE, so all users behind the CPE for that particular VC can access only one set ofservices. Users cannot select different sets of services, although using multiple VCs and establishing different PPP session on different VCs is possible
DIf a single IP address is provided to the CPE, and NAT or PAT is implemented,certain applications such as IPTV,which embed IP information in the payload, well not work. Additionally,if an IP subnet feature is used,an IP address also has to be reserved for the CPE
EPPPoA can use the features on the Cisco Service Selection Gateway (SSG)
正确答案: C,D解析: 暂无解析 -
第23题:
单选题Squeaky Beans Inc. hired an outside consultant to develop their web application. To finish the job quickly, the consultant created several dozen JSP pages that directly communicate with the database. The Squeaky business team has since purchased a set of business objects to model their system, and the Squeaky developer charged with maintaining the web application must now refactor all the JSPs to work with the new system. Which pattern can the developer use to solve this problem?()ATransfer Object
BService Locator
CIntercepting Filter
DBusiness Delegate
正确答案: B解析: 暂无解析
